This guide has the following sections:
- Introduction
- Questions to ask yourself first
- What am I going to use my new equipment for?
- How much do I want to spend (New/Used)?
- How frequently am I going to use it?
- Where am I going to use it?
- Do I have any dexterity/eyesight problems?
- What have I currently got and do I really need to change?
- Categories of Equipment
- Computers *
- Tablets ++
- Mobile Phones ++
- Printers**
** Nine times out of ten when someone asks me about buying a computer they will couple this with a request for advice about a printer to go with it. Therefore do look out for the third article Printers - What to get on this subject.
++ Other than some general comments about tablets & mobile phones I do not intend to cover them in much detail in this article but may return to them at a future date.
Introduction
Disclaimer. Before I begin I need to stress that there are no right or wrong answers when it comes to choosing computers and IT equipment. Any suggestions that I make are for guidance only and do not constitute recommendations to buy. However, I have many years’ experience in selecting and procuring equipment both in the public and private sectors as well as for personal use. I have learnt some hard lessons over the years that have instilled in me a number of maxims as follows:
- Think and plan before you buy.
- Draw up a budget and adhere to it.
- Remember that a higher price is not necessarily a guarantee of higher quality.
- Never be rushed into a decision for fear of missing an opportunity.
- Sticking to current, proven technologies is often more advisable than “trail-blazing” with the latest “must have”.
- Realise that the minute you have chosen and made your purchase there will always be something just that little bit better coming on to the market. Such is the pace of technological change that we have to accept the inevitability of this fact of life.
- Be honest with yourself when answering the key questions below.
What am I going to use my new equipment for? Whether your proposed purchase is a computer, a tablet, a mobile phone or a printer, decide what you want to do with it. If you just want a basic computer to enable you to send and receive emails; connect to and look up things on the internet; and write a few letters; there is no need to buy an all-singing all-dancing model. Most basic computers these days are pretty powerful and are well capable of meeting the demands of today’s universal requirements for shopping and video-calling.
Conversely, if you think you might be tempted to be more adventurous once you have got used to the item, don’t expect a basic machine suddenly to be capable of things like online gaming, high quality photography, online entertainment, videos and concerts. When buying technology it is definitely ‘horses for courses'.
How much do I want to spend (New/Used)? Deciding how much to spend on your purchase should not be limited just to the cost of the item itself. There is a factor in procurement, particularly of computers, called ‘Whole Life Cost’. Unfortunately, especially in public sector procurement, the WLC is not always counted in to the business decision. When working on a government computer procurement contract in the early 2000s, I was asked how cheaply I could purchase a computer for. I obtained a quote for a bulk purchase of a bottom of the range computer and communicated this cost. I had to explain that this did not include software; training; maintenance; power; planned replacements; etc. These are all factors that can make a huge difference to an investment decision. Sadly, the basic computer cost was the figure that appealed to senior staff anxious to demonstrate “efficient government procurement” and this was seized upon with glee! The hoped-for savings could never be achieved.
At the personal, domestic level it is still important to work out how much your computer is going to cost you over its life. If it is a printer for example, it is well known that the basic cost of one can be very low. Manufacturers often sell these “at cost” or less because they make their money from the subsequent purchase of printer ink. A key factor to examine therefore is the estimated ink usage per 100 sheets of paper and, hence, the number of new inks you will need to buy over the life of the printer.
Don’t necessarily discard the second-hand option. Bought from reliable sources, a used machine can offer a much higher specification and performance capability than a new one at a comparable cost. If you consider this alongside your planned use of the equipment, an older machine may be perfectly capable of meeting one's basic needs for a good number of years.
How frequently am I going to use it? You may not feel that this is an important factor but it can guide you to the sort of equipment to buy. If like me you spend a good proportion of the day at your computer, you need to buy something that meets your style of working. For example, if buying a laptop that has a small screen and will be used (literally) on your lap or a cushion tray, you need to consider the ergonomic aspects of the machine. If it becomes uncomfortable to stay at the screen for long then this is no good for an enthusiastic user who spends a long time working. A desktop computer is preferable as you can adapt the working position to your needs for lengthy periods.
Similarly, the amount of printing you plan to do can determine the size and position of your printer. If you rarely print anything, then a small portable printer can suffice. If you regularly print both colour and black and white and do quite a bit of copying, this will similarly have a bearing on your choice.
Where am I going to use it? Allied to the previous question is location. Will you regularly do your work at a desk or are you likely to take your equipment outside and on trips? Portability is obviously an issue for the latter.
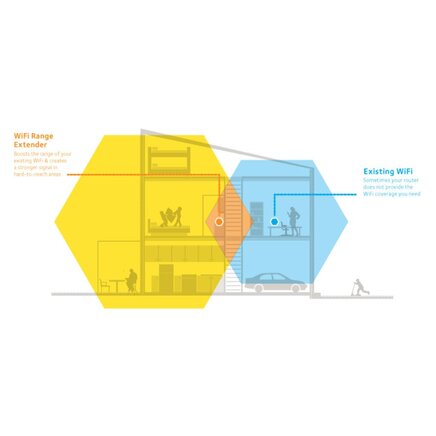
If you want to be able to use the computer anywhere in the house – sometimes downstairs and at other times in the bedroom – then relying simply on a desktop computer that usually needs to be in a fixed position will not be for you. Many people now take lots of photos and modern tablets and mobile phones have a capability that rivals high end cameras.
Do I have any dexterity or visual/hearing problems? If you have problems with (for example) arthritis or have visual or hearing impairment, these need to be taken into consideration – especially for the size of any keyboard and screen. Some printer controls can be quite “fiddly” and you need to be aware of this before buying. Hearing problems may call for special software or speakers, whilst people without any vision can still find equipment designed for the blind and partially-sighted.
What have I already got and do I really need to change? Sometimes it is a case of ‘better the devil you know’ and the attraction of a shiny new computer or tablet may be exciting but can bring with it a complete change to the way you have been used to working. A good example of this concerns the Windows operating system. It is well known that people used to earlier versions of Windows are often completely baffled when faced with the totally different layout (or User Interface as it is called) of the latest Windows 10. It is no surprise to learn that there is software available and regularly used that can make Windows 10 look like earlier versions.
If your desire to change is driven by frustration with the capabilities of your current computer, maybe you can consider updating some of the components of your present machine. You can add extra processing power and memory, buy a larger screen for your desktop, or add external storage if your current computer is getting full.
Summary. The military have a saying; “Time spent in reconnaissance is seldom time wasted.” Don’t rush into a buying decision without careful forward planning.
Categories of Equipment
This section of the article is about the various types of equipment you are likely to encounter and consider buying. I will look briefly at the following in turn:
- Computers
- Tablets
- Mobile Phones
- Printers
You may recall an earlier article of mine in which I looked at the history of computers and how they work. You can read it again here. These days computers are extremely powerful and come in all shapes and sizes. The Apple Watch on your wrist is a full-blown computer in its own right and is thousands of times more powerful than the computers that took the first man to the moon.
Generally speaking, a computer can be either a desktop, a laptop or a hand-held device. Desktop computers can be either a screen with a separate computer box (or tower) or – more commonly now – an All-in-One device that has the computer workings and storage built in to the screen itself. The All-in-One variety saves on space requirements and avoids the need for a lot of trailing cables underneath your desk. The one main drawback is that it is much more difficult to gain access to the workings of the computer should you need to repair if or wish to add further components.
On the left below is a tower desktop and on the right an All-in-One.
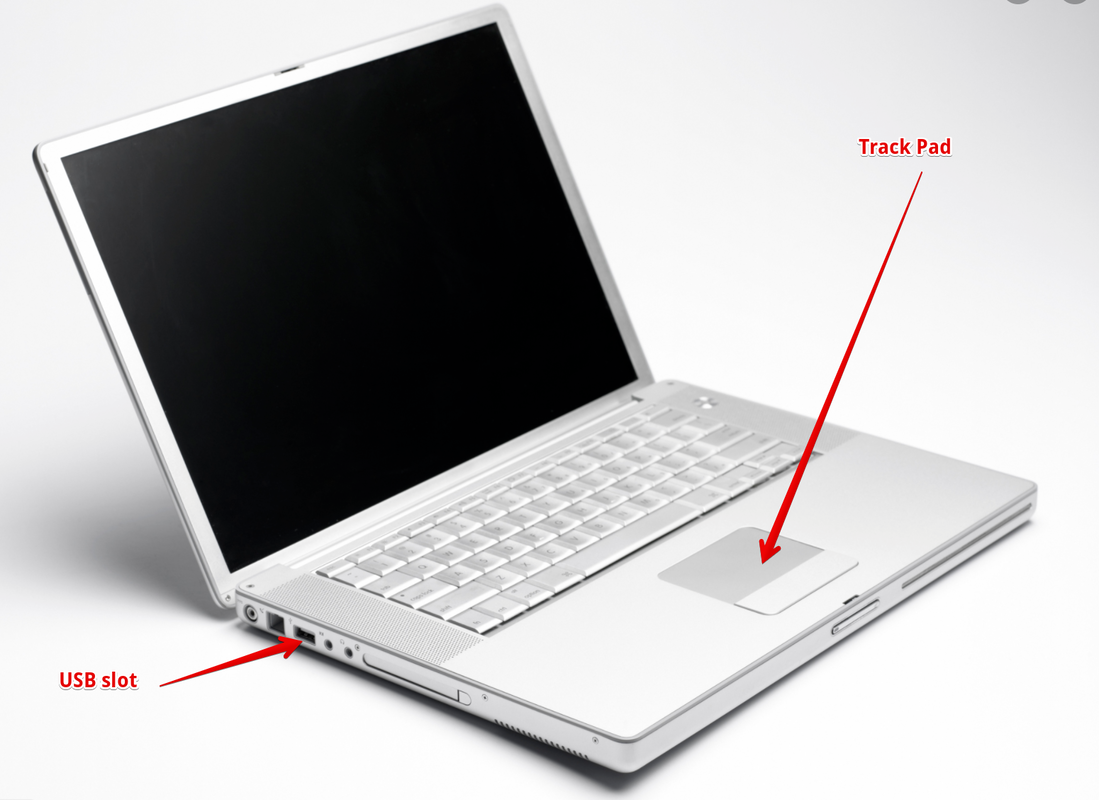
Laptops are easier to manage and are, of course, portable. Unlike a tower desktop they are difficult for the average user to access the working parts. There is a huge range of laptop computers and many are now becoming very similar to Tablets (see below) with the screen detachable from the keyboard. This provides the option to use the screen with touch entry or with conventional keyboard input. Laptops all have a built-in keyboard and mouse (the latter in the form of a track pad) whereas desktop computers require the addition of a separate keyboard and mouse. Not everyone likes the touch pad so you can always plug a mouse into the USB slot as in the picture below. The alternative detachable screen version is also depicted underneath.
Main things to look for
Computer come in a wide range of sizes, formats and capabilities. The three main things to consider are the size of the screen, the amount of processing power, and the quantity of data storage.
Screen The size of the screen you need will depend on your eyesight as well as the space you have available to position the computer. Screens these days are of exceptional quality, are usually flat and are light years away from the old cathode ray tubes. Like modern television sets, screens vary considerably in picture quality, clarity etc, so it always pays to view before you buy if at all possible.
Increasingly these days, input of data and “navigation” round the computer screen is by means of touch, using the fingers directly onto the screen. Anyone familiar with a computer tablet (see later) will already be adept at using a touch capability.
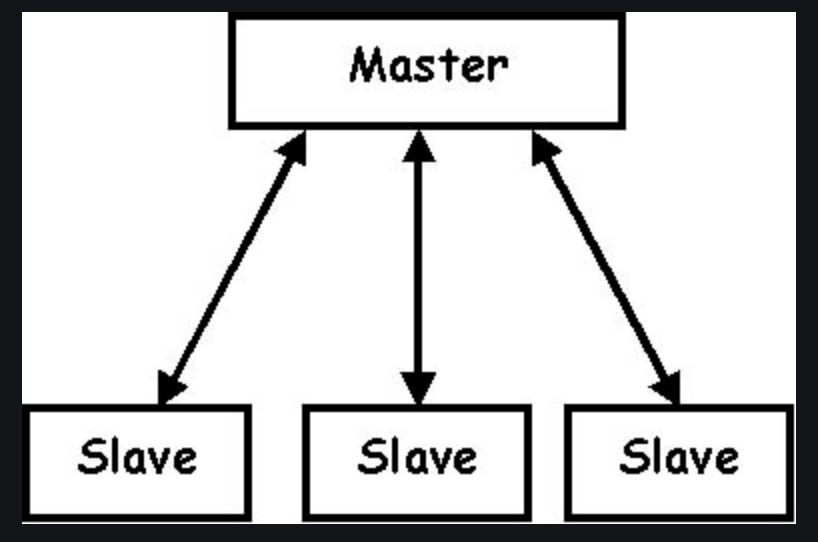
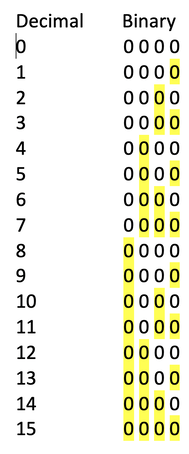
Processing Power The processing power of a computer comprises two components which are the ‘engine’ or “chip” and the memory. The chip governs the speed with which your machine can perform calculations and handle all the tasks the computer has to carry out. The memory is effectively the working space for the processor. This working space is referred to as Random Access Memory (RAM). Think of it as the space available on a physical desk/table top or work area. With a larger desk you can have a greater number of papers or books open around you as you work; a smaller desk means you will have to keep changing the position of your paperwork to be able to refer to it. With the computer, the size of RAM governs the amount of work the computer can carry out at one time without changing the contents of the memory. RAM is measured in Gigabytes. The more RAM you have the more work you can do at one time. Note, however, that if the RAM is not matched by an equally powerful processor chip the speed of your work will slow down. Consider 2GB of RAM as a minimum.
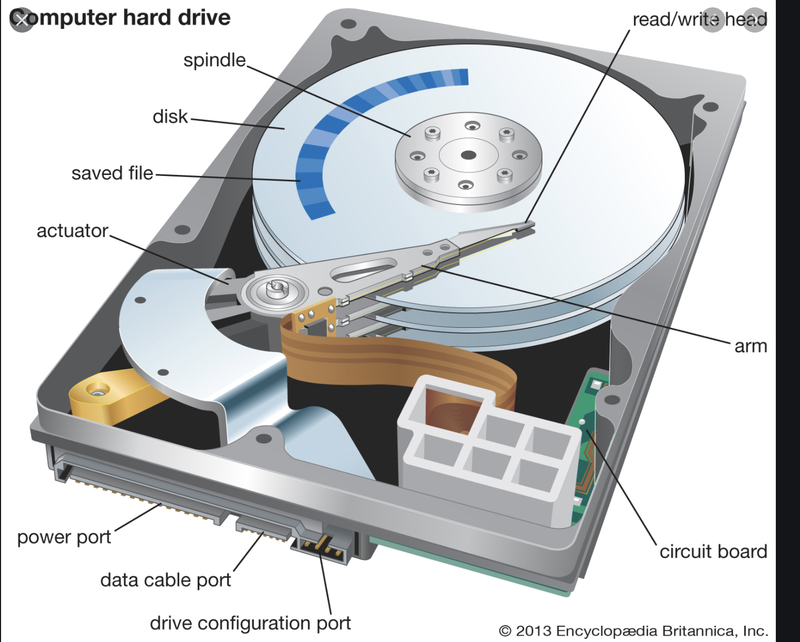
Data Storage Data storage is enabled on computers by means of internally-held storage facilities. In the past these were always in the form of a hard “drive” which was controlled by the computer and able to both read and write information to the stack of disks inside the drive. Here is a picture of a typical computer hard disk drive (HDD) and, alongside, an exploded diagram showing the inner workings with moveable read/write arms.
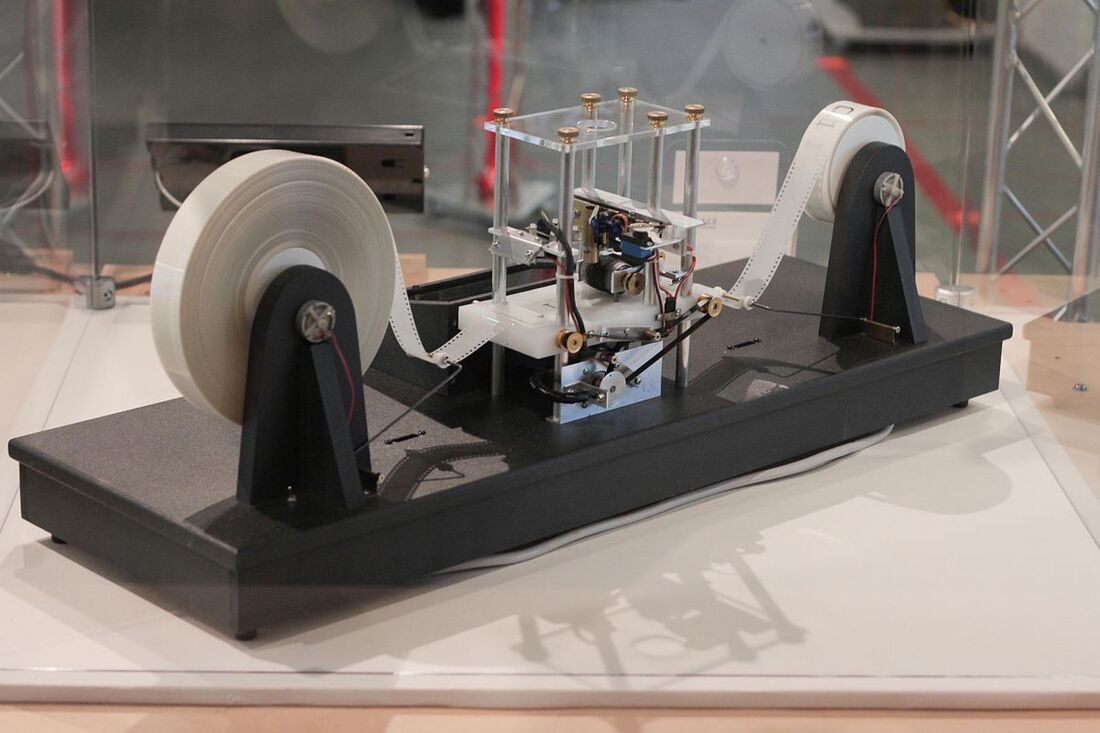
Increasingly, internal (and external) storage disks are built not as a stack of hard round plates with moveable read/write arms (as in the above picture) but in what is called Solid State. This consists of an array of silicon chips with no moving parts. A Solid State Drive (SSD) is smaller and more reliable but does cost a little more.
Tablets
I mentioned earlier that more and more computers these days have a touch capability enabled. This capability gave rise to a blossoming market for the sale of tablets. Indeed, for many people these days a tablet might be their first introduction to computers. Having a desktop or laptop computer is now by no means a pre-requisite to being able to carry out all the functions previously only possible on a larger computer.
Tablets are now very much in our common vocabulary. The original tablet was the Apple iPad but many other varieties now exist. However, to some extent the Apple nomenclature has entered everyday language and you may hear reference to an iPad even if it is made by another manufacturer such as Samsung.
As I have depicted above, some machines on the market today are built with a dual functionality; they can be operated very much as a laptop or the screen can be “flipped” or detached and perform as a tablet.
I do not propose to go into any detail on tablets in this article but may return to it at some future occasion.
Mobile Phones
No article on computers could be complete without mentioning mobile phones. Though they were very different bits of equipment in the past, mobile phones these days are essentially computers in their own right. Many look just like a mini tablet and can perform most of the same functions. We have come a very long way from the original telephone.
Nine times out of ten when someone asks me about buying a computer they will couple this with a request for advice about a printer to go with it. As with some of the other topics in this article, I will not delve into printers but look out for a future article on them.